How it works
Threats & protection
Zebra Sharing System provides adjustable level of security. You can find your balance between usability and data protection.
|
Longer key Configuration of key length is flexible and smart |
SSL certificate HTTPS is strongly recommended in any case |
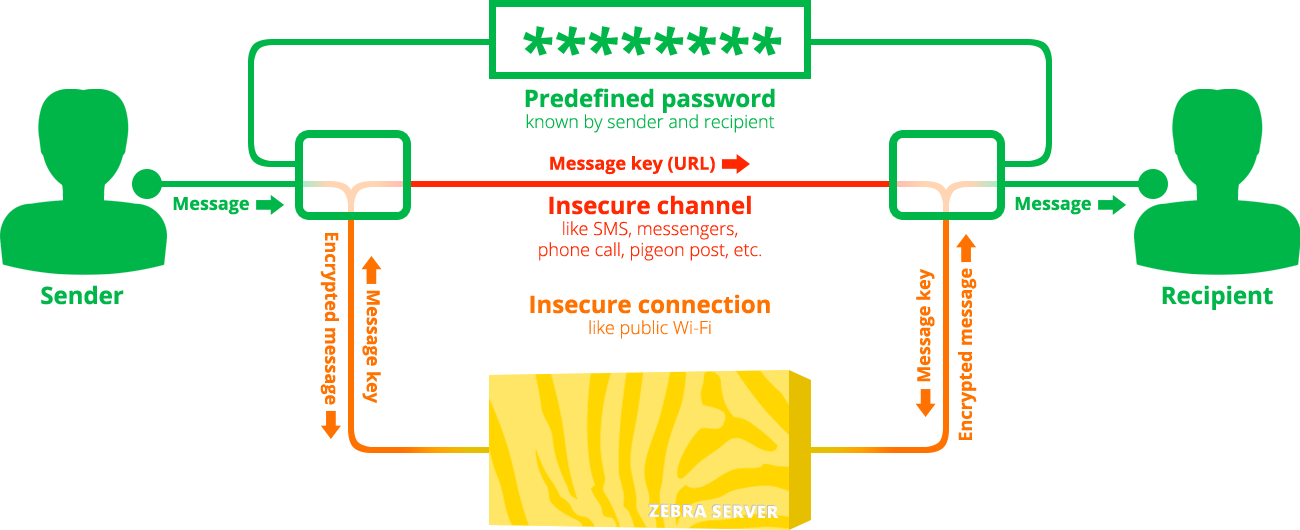
Client-side password Encrypt data on client, so server will not have original data at all |
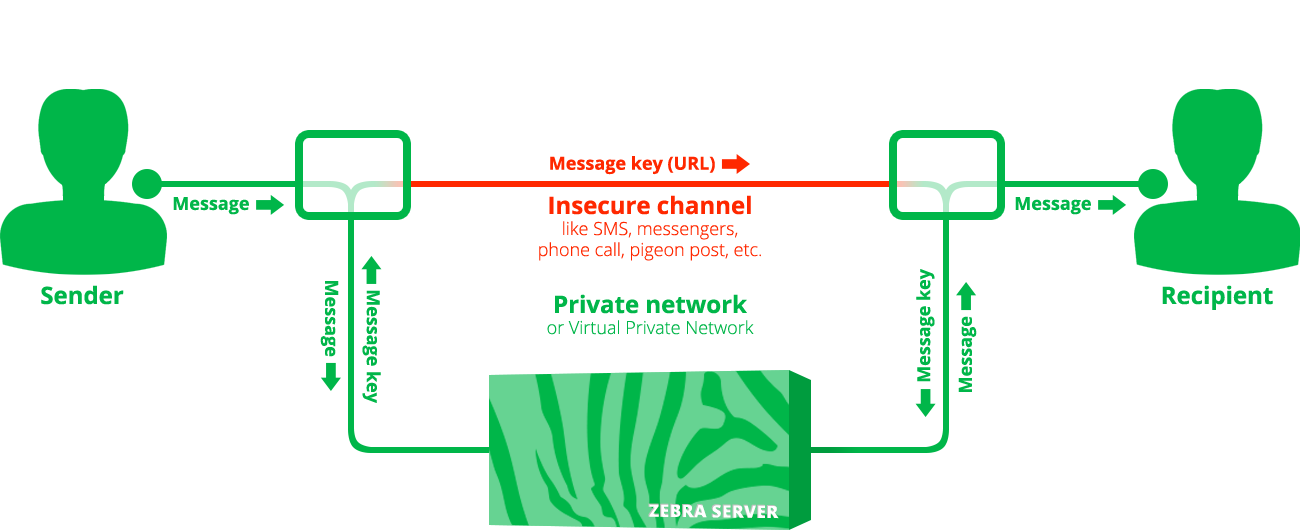
Private network Run Zebra in private network and it will be protected on network level |
Local client You can easily run HTML client from your own device |
API key If you have limited number of users, give them keys to use Zebra |
Access password Protect you shared data via password on server side |
|
|---|---|---|---|---|---|---|---|
| Insecure network. Man-in-the-middle attack or network sniffer is a problem, so you need to be sure that if somebody collects your traffic, he will not be able to read it. | ✓ | ✓ | ✓ | ||||
| Unsafe channel for key delivery. You send link with key via SMS, Slack, Telegram, etc. Does it look absolutely safe for you? | ✓ | ✓ | ✓ | ✓ | |||
| Compromised server. Somebody hacked your infrastructure and has access to Zebra code or Redis storage. Not good, but not a tragedy. | ✓ | ||||||
| Compromised client. Somebody hacked your infrastructure and modified Zebra client not to use encryption or send data somewhere else. | ✓ | ||||||
| Key brute force. Zebra has rate-limiting logic, but there are some more ways to protect shared data from key brute force. | ✓ | ✓ | ✓ | ✓ |
-
Zebra API
github.com/charger88/zebra-api
The main component, obviously. It is Go lang application, which handles server-side part of the functionality. You can use it from some your applications without Zebra Client.
-
Zebra Client
github.com/charger88/zebra-client
HTML single page app (ES6, so old browsers are not supported) which may be served by web server or may be opened as HTML file from local disc.
-
Docker images
github.com/charger88/zebra-docker
Possible way to run Zebra API and Zebra Client. Even if you are going to run Zebra not in Docker you anyway may find some useful information there.
Run your own
There are some ways to run your Zebra instance. Detailed documentation may be found in the git repositories in readme files.
Way 1. As separate docker containers
- Clone https://github.com/charger88/zebra-docker
- Customize if needed
- Run
docker-compose up
You can run it in cloud container service like AWS ECS, but you may need to read some about Docker and AWS ECS.
Way 2. Run components manually
- Run Redis server instance
- Install Go language and required components. Look at the dockerfile for details
- Clone API https://github.com/charger88/zebra-api
- Customize config if needed
- Run Go application
go run *.go - Clone client https://github.com/charger88/zebra-client
- Install and configure nginx (or another web server). Config example.
